Question 1: How can we secure operations of” Institute of Computing”, KUST through applying various
security layers.
Answer:
We can secure operations of the Institute of Computing “KUST” by applying the following
security layers.
Physical Security:
Physical Security is necessary everywhere in the world even in the Institute of Computing “KUST”.
By applying Physical Security we can minimize the risk.
Secure Networks and Systems:
We can secure operations of the Institute of Computing Kust by its networks and Systems.
Vulnerability Programs:
We can secure the operations of the Institute of Computing by avoiding using
vulnerable programs or we should patch the vulnerability in those programs before using them.
Strong Access Control Measures:
We can secure operations of the Institute of Computing by applying Strong Access Control
Measures. There are some types of access control like
Role-Based Access Control (RBAC)
Discretionary Access Control (DAC)
Mandatory Access Control (MAC)
Protect and Backup Data:
We can secure operations of Institute of Computing by protecting and take
Back up it’s data regularly. Because by taking backup regularly even when data
Of Institute of Computing effected by any ransomware then we can continue
Our normal operations by restoring our backup.
Monitor and Test Systems:
We can secure operations of the Institute of Computing by constantly monitoring
and testing our systems. If regularly monitor our system then it will help us to
find any intruders that are trying to enter into our systems.
Regularly testing our systems help us to find any vulnerability that will be
The cause of an attack in the future. So If we find those vulnerabilities before
It becomes a zero-day. Patch those vulnerabilities so no one will be able to attack.
This is the question 1 solution of information security paper. Like us on Facebook in order to get technology updates and free courses everyday.
Check Database Management System Paper Solution
Question 2: If Confedentiliaty of Online Result on KCMS is Compromised before the declaration of results
then what would be its effects on the result?
Answer:
Confidentiality means when information is disclosed to an unauthorized person or information
is leaked to an unauthorized person. If the confidentiality of online result on KCMS is compromised
before the declaration of results then only the attacker or intruder who have hacked the
confidentiality of the result so that person will be able to to see the result.
This is his or her choice if he wants to disclose the result to another person on the university or he/she
want to keep it secret.
If the attacker discloses information with other people in the university then other
people will know about the result before the official announcement of that result. If only
confidentiality is compromised then no such harming effect will happen on the result but if
Integrity is compromised then will cause a dangerous effect on the result.
we secure operations
Question 3: If an attacker wants to get information about a particular student in BSCS 6th student
from KCMS. Which type of attack would be better either active or passive. And Why?
Answer:
If any attacker wants to get information about a particular student in BSCS 6th student from
KCMS passive attack
Would be better because
Reason:
Passive attack would be better because
Active attack target integrity and availability, user is disturbed, data
Is captured or snipped and there is change in the data occur.
While passive attack only target confidentiality of user and user is not
Disturbed and only data is snipped or captured here.
- A passive attack is the first phase of attack after information gathering.
- There are fewer chances get caught in the passive attack
Question 5: Which type of access control would be better to secure KCMS and Why?
Answer:
Role-based access control would be better to secure KCMS Because:
Reason:
This access control grants access to users on the basis of the user’s job function.
Users are permitted on the basis of their role in an organization. Accountants will gain access to
financial information only.
Faculty members will gain access to the subjects assigned and to the student’s attendance
and exam only.
That’s why Role-based access control would be better to secure KCMS.
Students will have access to check their attendance, marks, and their other data on KCMS.
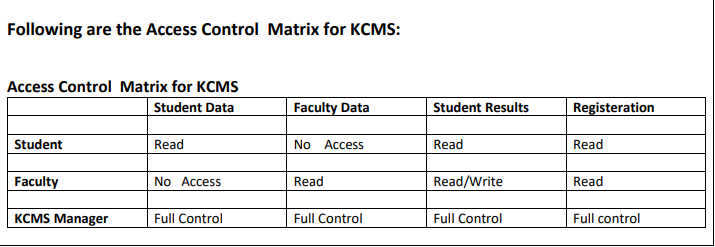
Question 6: Create an Access Control Matrix for KCMS. Users in this Access Control Matrix are
students, faculty, KCMS Manager. Objects are students and faculty data and students results and registration.
Answer:
Contact us on Facebook If you want to solve your paper.
